Domain Join and Group Policy
When you think about it, traditional home‑based Windows PCs are unmanaged in the sense that there’s no central oversight available, either by the head of a household or a central server. This type of computing, which has been formally described as workgroup computing makes a certain amount of sense at home, where each PC is an island of functionality onto itself. In the workplace, however, especially at mid‑sized businesses and enterprises where there can be hundreds or thousands of PCs, the go‑your‑own route doesn’t actually make any sense. Corporations need a central way to manage users, PCs, devices, and other entities, and ways to secure and update their computing products. They need what’s called a managed solution.
The most popular managed solution for businesses is called Active Directory, or AD. It requires a centralized Windows Server infrastructure and uses Group Policy to establish rules for its computing services. While AD and Group Policy haven’t made a lot of headway with smaller businesses–though that could change with the adoption of these services in cloud‑based solutions like Windows Azure, Office 365, and Windows Intune–it’s the standard at larger businesses. And chances are, if you’re provided with a PC at work, you’ll be required to sign in to your AD domain, not just to the PC using a local account or Microsoft account. Domain joined computers are controlled via policy, so they can be very restrictive, especially for such things as application installation and certain system customizations. But they’re also typically better locked down from a security standpoint and, when configured properly, allow you to access your company’s secure network resources, even while working remotely.
Domain join works in Windows 8 as it did in previous Windows versions. If your Windows 8 PC hasn’t been pre‑configured with your user account, you can sign in to the domain in two ways: from the lock screen or through the Advanced System Properties control panel.
To sign in to your domain from the lock screen, select Other user. Then, in the screen shown in Figure 14‑1, you must provide your domain, username, and password credentials.
Figure 14‑1: Signing in to a domain from the Windows 8 lock screen
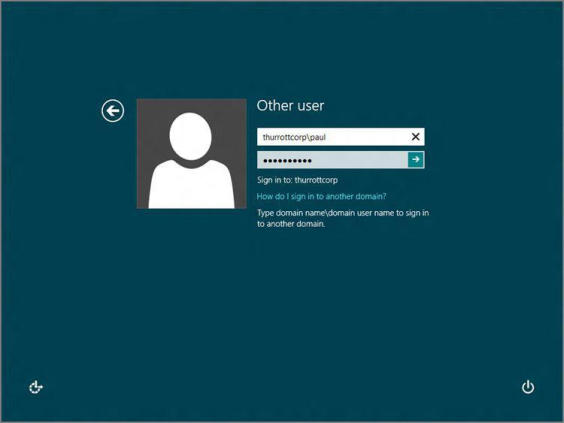
This sign‑in must take a specific form, like domain\username or username@domain , in the username field. (Your employer will provide the domain name.) Assuming the domain name is mydomain.com and the username is paul , the username would then be mydomain\paul or paul@mydomain.com .
Alternatively, you can connect to your domain first from a local (or Microsoft) account using the Advanced System Properties control panel. You might use this method if you wanted to access your work account from your own home PC, for example, though again your workplace would likely provide you with additional tools (such as a VPN) or information for making the connection.
First, of course, you must find Advanced System Properties. The easiest way is to use Start Search from the Start screen, type advanced system , and then choose Settings from the Search bar. In the search results list, select View advanced system settings. You’ll see a window like the one in Figure 14‑2. (If not, navigate to the Computer Name tab.)
Figure 14‑2: Advanced System Properties
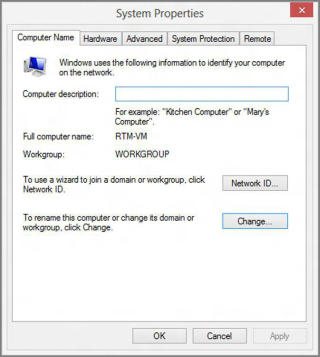
To sign in to your domain, click Change. In the Computer Name/Domain Changes window, enable Domain and type your fully qualified domain name (yourdomain.com ) in the Domain field. (Again, this will be supplied by work.) Then, in the dialog that appears, type your username only (for example, paul , and not mydomain\paul ) and password. You’ll be prompted to log off and then sign in with the new domain account. Here, again, you’ll need to use either the domain\username or username@domain.com syntax for the username (for example, mydomain\paul ).
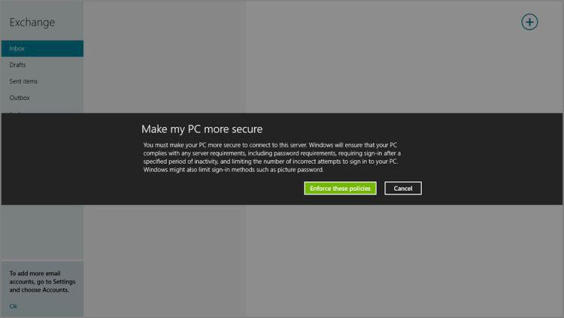
When you sign in with a domain, Windows 8 works largely as it does otherwise, aside from whatever policy‑based limitations your corporation has applied. Two obvious areas of difference include the new Metro‑style Mail app, which is discussed in Chapter 8: When you run this app, you may be required to accept the workplace’s more stringent Exchange ActiveSync (EAS)‑based policy, as you can see in Figure 14‑3. This requirement exists outside of whatever domain‑based policies you may have in place as well.
Figure 14‑3: EAS clients like Mail app will be required to conform to your workplace’s policies before they can be used with a work‑based account.
Likewise, the User Account control panels work differently with a domain. We discuss these differences in Chapter 12.
Дата добавления: 2015-05-13; просмотров: 1319;
